What HTTPS-Only Browsing Means for the Future of Direct Carrier Billing
Sometimes a single technical change forces an entire industry to rethink how it operates.
From October 2026, Google Chrome’s move to HTTPS-only browsing will do exactly that for Direct Carrier Billing.
There will be early signs of impact before then, as enhanced security settings roll out to segments of users. But the direction is clear. The model the ecosystem has relied on for years is changing.
On the surface, this update is positive. It strengthens privacy, improves security, and aligns with regulatory expectations.
But it also challenges one of the core mechanisms that DCB depends on.
Header Enrichment and the Conversion Model
Header Enrichment has been central to how DCB delivers high conversion rates.
A user clicks. The network identifies them. The subscription completes.
That simplicity is what makes it commercially powerful.
But it relies on the ability for operators to access and modify request data as it passes through the network. In an HTTPS-only environment, that visibility disappears. The connection is encrypted end-to-end before headers can be accessed.
Which means Header Enrichment, as it exists today, no longer functions.
From Seamless to Fragmented Journeys
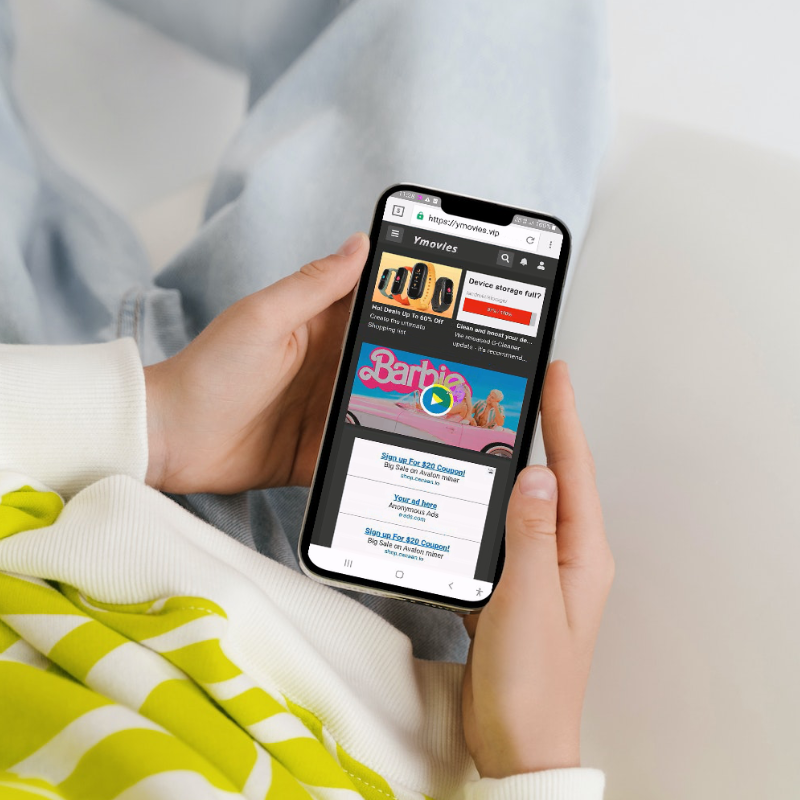
When Header Enrichment fails, the user journey changes.
Instead of a single interaction, users are likely to face multi-step authentication:
- Entering a mobile number
- Receiving an OTP
- Entering a verification code
- Or interacting with token-based identity flows
This isn’t just a technical adjustment. It’s a shift from near-instant conversion to a process that can take several steps.
And in practice, that doesn’t always look like “friction.”
Often, it looks like failure.
A user clicks “subscribe,” nothing happens, or they’re redirected into a flow they weren’t expecting. In many cases, they simply drop off.
That’s where the real commercial impact sits.
Impact Across the DCB Ecosystem
This change doesn’t sit in one part of the value chain. It affects all of it.
Content providers will need to redesign and optimise flows to recover conversion rates that were previously driven by one-click.
Aggregators will need to support multiple identification methods at once, while maintaining consistent reporting, attribution, and partner visibility.
Operators face both risk and opportunity. Delayed adaptation means lost revenue. But there is also a clear opportunity to define how secure, standardised identity works in this new environment.
Regulators are likely to support the move towards HTTPS, but scrutiny around identity handling, consent, and data processing will increase.
Anti-fraud providers will need to adapt quickly. As Header Enrichment becomes less reliable, fraud will shift towards OTP abuse, token manipulation, and social engineering.
Traffic providers and DSPs will also feel the impact, particularly where attribution becomes less reliable due to broken or inconsistent flows.
No Single Solution, But Clear Directions
There is no single agreed approach emerging yet, but several clear directions.
Some players are exploring TLS proxy models, recreating Header Enrichment within encrypted environments, although this raises privacy and trust concerns.
Others are moving towards token-based identity, where subscriber validation happens through secure tokens rather than exposed identifiers.
There is also growing momentum behind API-based approaches, including GSMA Open Gateway initiatives, which aim to standardise identity in a way that is interoperable and privacy-aligned.
This isn’t just a technical decision. It affects commercial models, user experience, compliance, and scalability.
The View from MCP Insight
At MCP Insight, we’re already working closely with partners across the value chain to understand how this plays out in real environments.
Where are flows breaking? What happens to conversion when fallback mechanisms are introduced? How do fraud patterns change when authentication shifts? What level of visibility is lost, and how can it be recovered?
Because while the mechanisms are changing, the objectives are not.
- You still need to maintain revenue.
- You still need to detect and prevent fraud.
- You still need to demonstrate compliance.
- And you still need a clear, accurate view of what’s happening across your markets.
What changes is how you achieve that.
Our focus is on ensuring that, regardless of which identification models emerge, our clients retain the insight and control they need to operate confidently.
Welcome to the HTTPS Era
There’s a tendency to view this as a technical hurdle to overcome.
It’s more than that.
Header Enrichment has been a defining feature of DCB for years. Moving away from it isn’t just an adjustment. It’s a seismic shift in how identity, consent, and conversion are handled across the ecosystem.
Handled well, this transition could lead to more secure, standardised, and transparent models. Handled poorly, it risks fragmentation, reduced performance, and increased exposure to fraud.
At MCP Insight, we’re already working closely with partners across the value chain to understand how this plays out in real environments.