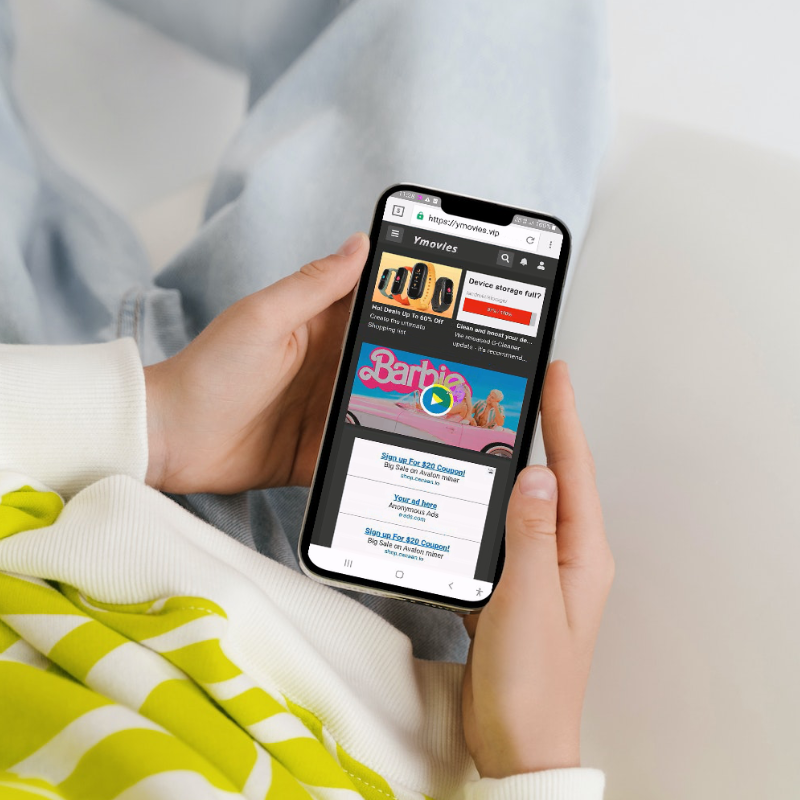
MCP’s fraud investigations team has noticed app malware activation patterns changing over the last 3 years. MCP identifies suspicious apps promoted to users via advertising seen in its Scanner monitoring tool. These apps are downloaded onto mobile devices to replicate the User experience. To a User, the advert and app look normal. More often than not, the app will have 100,000+ downloads and be on a popular app store such as Google.
In early 2019 70% of malware apps downloaded, generated fraud upon immediate download (payment for a service unknown or not consented to by the consumer). The first a User knows of this fraud is when a billed receipt arrives (but this is often suppressed by the app malware) or they see deduction from their mobile bill.
By 2021 this fraud pattern has changed to just 11% fraud generated within 24hrs or upon download. The incubation or sleep time before malware acts or the device is infected is increasingly over longer periods, with 23% now activating after 30 days.
Intel generated from app malware investigations is used to support investment in Shield (MCP’s auto-block anti-fraud tool), ensuring it keeps up with an ever more sophisticated app malware environment.
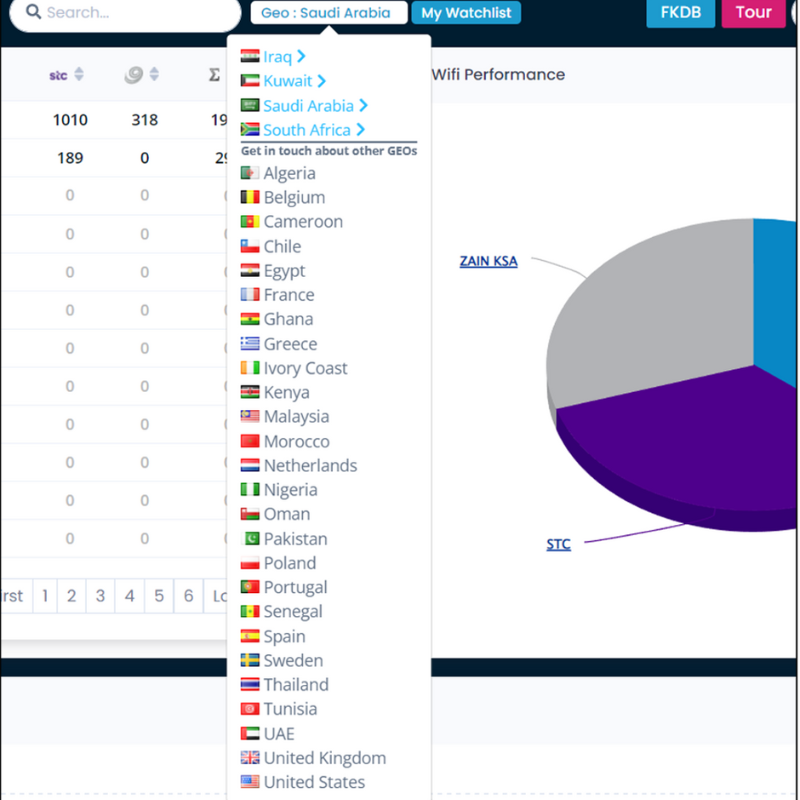
MCP Insight is a UK-based compliance and fraud monitoring company, specialising in mobile gateway traffic. Our clients include Mobile Operators, Regulators, Aggregators, and Merchants. We’ve been providing solutions to the mobile payments industry across 30 territories for the past six years.